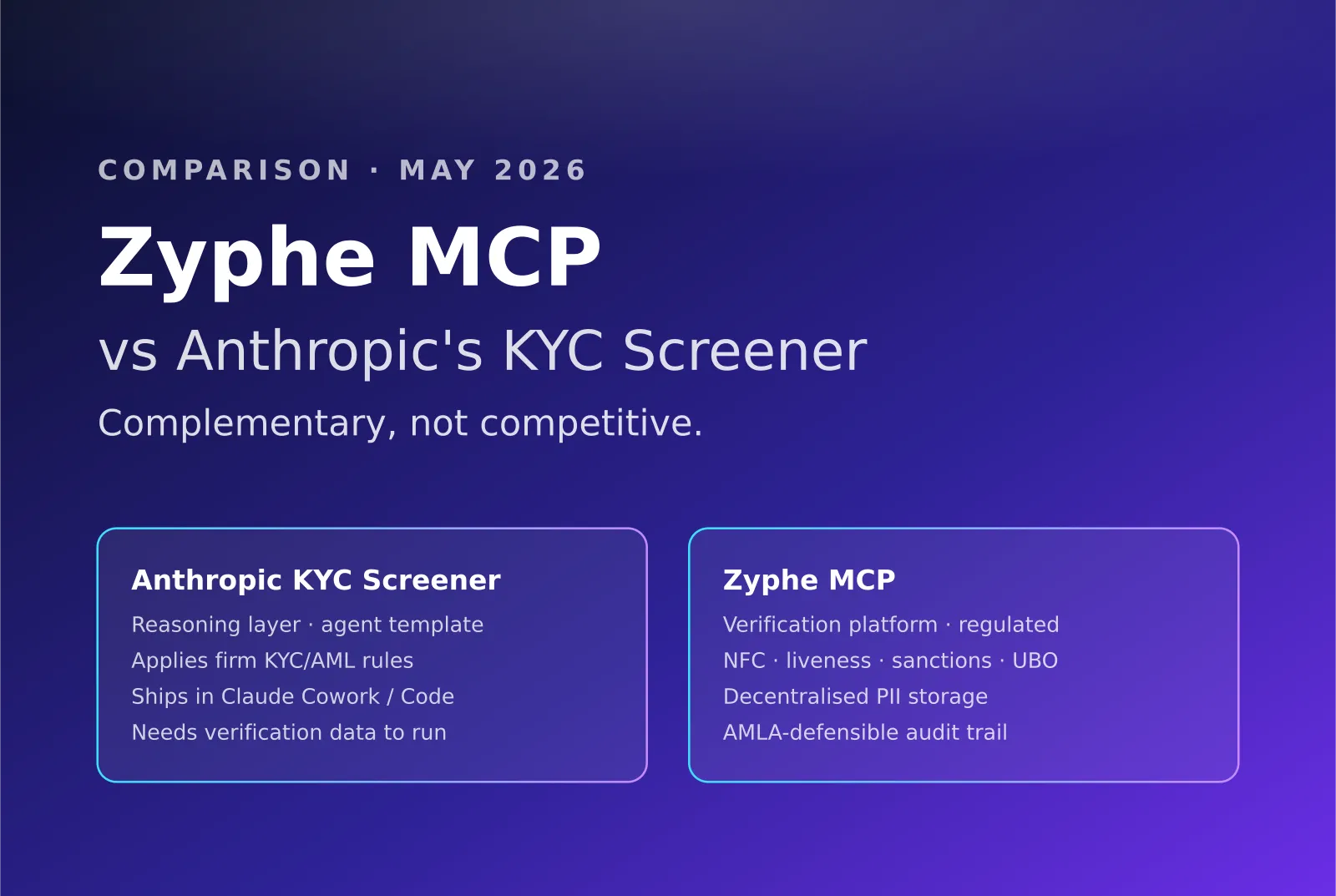
Anthropic's KYC Screener is an agent template. Zyphe MCP is the platform under it. Complementary, not competitive — side-by-side breakdown.
Table of contents
TL;DR
On May 5, 2026, Anthropic released ten ready-to-run agent templates for financial services, including a KYC Screener agent (kyc-screener) with a built-in kyc-rules skill that applies a firm's KYC/AML rules to onboarding records. Anthropic also expanded the partner ecosystem with new MCP apps, including a Moody's MCP app that brings credit ratings and data on 600 million+ public and private companies. The same week, Zyphe shipped native Model Context Protocol support that lets compliance and product teams build, change, and operate the underlying identity-verification platform through their AI assistant. The two products operate at different layers of the stack. Anthropic's KYC Screener is the reasoning layer (the agent that decides). Zyphe MCP is the verification layer (the platform that performs). A regulated firm running Anthropic's KYC Screener on top of Zyphe gets the best of both: agentic judgment over real, regulator-defensible verification data with decentralised PII storage.
Reading time: ~9 minutes · Last updated: May 7, 2026
What did Anthropic actually launch on May 5, 2026?
Anthropic's May 5, 2026 announcement covered three things relevant to compliance teams.
Ten financial-services agent templates. Ready-to-run agent templates for time-consuming work in financial services, including the KYC Screener, month-end close, and others. Each agent ships as a plugin in Claude Cowork and Claude Code, and as a cookbook for Claude Managed Agents.
The KYC Screener specifically. An agent template that includes a kyc-rules skill describing how Claude should apply a firm's KYC/AML rules to a parsed onboarding record. The agent assembles entity files, reviews source documents, applies the firm's own rules, assigns risk ratings, and packages escalations for compliance review.
Expanded MCP partner ecosystem. New connectors and an MCP app ecosystem so the agents can draw on the data financial professionals already use. Moody's launched an MCP app that brings proprietary credit ratings and data on more than 600 million public and private companies for compliance, credit analysis, and business development.
This is distinct from the other Anthropic launch that compliance buyers sometimes confuse it with: Anthropic's Persona-based identity verification for Claude users, rolled out in April 2026. That product asks users for government ID and a selfie before allowing certain features. It applies to end-users of Claude, not to the regulated firms who use Claude to do compliance work.
This piece is about the May 5, 2026 finance-agents launch (the KYC Screener), not the April 2026 user-identity-verification feature.
What did Zyphe ship in the same week?
In the same week, Zyphe shipped native Model Context Protocol support that exposes the entire Zyphe identity-verification platform to any MCP-compatible AI assistant. Compliance and product teams can now build, change, and launch onboarding flows by talking to their AI assistant; manage AML cases through natural language; carry company policies from Notion, Confluence, or wikis directly into Zyphe configurations; and provision the developer credentials engineering needs to embed verification into their app.
For the full launch detail, see our Zyphe MCP launch news article.
The launch architecture is: dedicated service identity per assistant, scoped permissions, audit trail identical to dashboard-driven actions, instant credential revocation. The team's existing AI assistant (the one that already knows the team's product, Slack, Notion, codebase, and brand voice) gets hands inside Zyphe.
Why are these complementary rather than competitive?
The most important point procurement teams should hold onto is that Anthropic's KYC Screener and Zyphe MCP are layers of the same stack, not alternatives to each other.
Anthropic's KYC Screener is a reasoning layer. It is an agent template, a Claude-based assistant with a kyc-rules skill, that takes a parsed onboarding record, applies firm-specific rules, and produces a risk rating. It is excellent at the parts of compliance work that involve judgment over structured information.
Zyphe is a verification platform. It performs actual identity verification (NFC chip read on passports, two-step biometric liveness with deepfake detection, sanctions and PEP screening across 230+ European corporate-registry databases plus equivalent US/LATAM/APAC coverage in 190 countries, decentralised per-region PII storage, regulator-defensible audit trail). It is the layer that answers "did this person actually verify, and what does the regulator-readable evidence say?"
The KYC Screener needs verification data to do anything useful. Without an underlying compliance platform feeding it real verification results, sanctions hits, registry data, and policy-applied evidence, the agent is reasoning over nothing. With a platform like Zyphe behind it, exposed through MCP, the agent has the substrate.
Manuel Tumiati, Zyphe's CTO and co-founder, has framed it with live clients: agents perform those triage tracks already, and the false-positive review work that compliance used to do by hand is automated on Zyphe's side. The agent layer Anthropic just productised externally is the same architectural pattern Zyphe has been running internally for months. Anthropic standardised it; Zyphe runs the platform underneath it.
Where exactly do the two products differ?
A side-by-side comparison across the dimensions procurement teams actually evaluate.
The comparison clarifies the relationship: Anthropic's KYC Screener is a smart agent that needs a platform. Zyphe MCP is the platform.
How would a regulated firm combine both?
The natural combined deployment is a four-layer stack. Each layer keeps doing what it is good at. The regulator audits the whole chain, not any single layer in isolation.
- Verification platform (Zyphe). Runs in production as the firm's KYC/AML system of record. NFC chip read, two-step liveness, sanctions screening, UBO walking, decentralised PII storage, per-decision audit trail. This is where the regulator's evidence sits.
- Open protocol (MCP). Exposes the platform to any compliant client. Service-identity-scoped, full audit trail, instant revocation. Same protocol whether the calling client is Claude, Cursor, ChatGPT, an internal agent, or a future model the firm has not yet adopted.
- Agent template (Anthropic's KYC Screener, or equivalent). Reasons over the verification results, sanctions hits, UBO trees, and firm policies retrieved through MCP. Applies the firm's
kyc-rulesskill on top of that data. Produces a risk rating and an escalation packet. - Human reviewer (MLRO, compliance officer, board sign-off). Approves the agent's recommendation. Owns the regulatory accountability the regulator personally asks about under FCA SMCR and AMLA per-decision defensibility frameworks. The agent does not replace this layer; it removes the assembly work that used to consume it.
The compliance team operates the verification platform through their existing AI assistant via Zyphe MCP, building flows, configuring policies, and triaging cases through conversation. When the firm wants Claude-driven agentic compliance work, it deploys Anthropic's KYC Screener (or any other agent template), which calls Zyphe MCP tools to retrieve verification results and policy-applied evidence. The agent's reasoning is grounded in regulator-defensible data rather than synthetic or partial information. The verification is performed by a regulated provider with EU/UK/US compliance posture and decentralised storage. The audit trail covers the agent's decisions and the platform's verifications end to end.
This is the architectural pattern we expect to dominate compliance work over the next 18 months. Agent templates standardise the reasoning layer. Open-protocol MCP lets agents call platforms. Platforms (Zyphe, Moody's, others) provide the regulated data and the audit-ready evidence the regulator actually wants to see. Firms that implement only the agent layer will find their auditors asking where the verification evidence comes from. Firms that implement only the platform layer will keep paying analysts to do assembly work the agent could do better.
What does the underlying identity-verification stack look like at Zyphe?
For procurement teams evaluating whether Zyphe is the right verification platform under any AI agent (Anthropic, OpenAI, Google, internal), here is the stack that an agent calls into when it uses Zyphe MCP.
Identity verification. NFC chip read from passports and ID cards (ICAO 9303 and eIDAS-compatible). Two-step biometric liveness: passive micro-movement detection plus active consistency check for deepfake detection. No image upload allowed during the verification flow (the system captures 10-15 photos itself to prevent fraud). One-click re-verification for users already in the Zyphe credential network (passkey or biometric short-flow).
KYB and UBO walking. Direct integration with 230+ European corporate-registry databases plus US state Secretary of State APIs, ACRA Singapore, DIFC, and equivalent registries across 190 countries. Recursive UBO trace down to 0.001% ownership thresholds. Group-structure visualisation for multinational corporate customers. Where the structure terminates in opaque jurisdictions (BVI, Cayman, Marshall Islands), Zyphe's specialist agent flags the opacity and surfaces residual signals from adjacent layers.
AML automation. Sanctions screening across World-Check, Comply Advantage-equivalent feeds, OFAC, EU consolidated, UK OFSI, UN, and government-direct lists. Adverse media checks. Internal agent triage so that only true-positive matches surface to compliance officers, eliminating the false-positive review cycle that ate analyst time on legacy platforms. Manuel Tumiati framed the architecture with live clients: Zyphe combines fixed internal risk factors used to compute its own risk score with customer-customisable factors such as jurisdiction and country of provenance, screens the UBOs, and runs an adverse media check.
Decentralised storage. Source documents are sharded across 60,000+ decentralised storage nodes using a 29-of-100 threshold scheme, with per-region data residency (Switzerland data stays in Switzerland, Singapore data stays in Singapore, EU data stays in EU member states). The customer holds the encryption key. Zyphe has no master key. The IDmerit-shaped breach exposure that justified Anthropic's careful Persona partnership for end-user verification disappears at the architecture layer.
Audit-trail reproducibility. Every verification, every credential issuance, every revocation, every alert, every triage decision lands in an immutable case file. AMLA per-decision defensibility, FCA SMCR personal accountability, FinCEN reasonably-designed standard, and the corresponding documentation requirements all sit on top of this primitive.
When an Anthropic KYC Screener agent (or any other MCP-compatible agent) calls Zyphe through MCP, it gets all of this as structured tool responses. The agent reasons. The platform verifies. The regulator audits the chain.
When might the combined stack not be the right pattern?
We have argued the case for combining the two. In the spirit of giving procurement teams an honest read, here are the situations where the combined Anthropic KYC Screener plus Zyphe MCP pattern is the wrong fit.
The firm has not yet matured its compliance policies. Agent reasoning over policy assumes the policy is documented and consistent enough to be applied. Firms that are still drafting their first MLRO Manual or whose risk-tier matrix lives in a single person's head should harden the policy first. The agent will faithfully reproduce whatever ambiguity is in the source.
The firm operates in a regulated regime that has not yet recognised AI agent-driven compliance work. A small number of jurisdictions (and a smaller number of supervisory authorities within them) still expect a named human to produce specific compliance artefacts unaided. The combined stack still works, but the firm should treat the agent's output as input to a human-authored decision rather than the decision itself. Where the firm operates under FCA SMCR or AMLA per-decision defensibility, the human-in-the-loop layer in our four-layer stack handles this cleanly.
Verification volume is too low to justify the integration. A firm that onboards 50 customers a month and has no growth plan will not feel the difference. The combined stack pays back at scale, when assembly work consumes meaningful analyst time. Below that threshold, dashboard-driven Zyphe with manual case management may be the right pattern for another year.
The firm's data residency or sovereignty requirements rule out the agent platform. Some regulators require that all compliance reasoning happen inside specific jurisdictional boundaries. Anthropic publishes its data-processing geography; firms with strict requirements should verify before deploying the agent template. Zyphe's per-region decentralised storage handles this at the verification layer; the agent layer is the firm's responsibility to validate.
If none of these caveats apply, the combined stack is the right pattern. If one or more do, the firm should still adopt the verification platform first (so the data is regulator-defensible from day one) and add the agent layer when the constraints lift.
How should procurement teams evaluate both?
Five concrete moves.
- Map the layers correctly. Decide which layer each product covers in your stack. Anthropic's KYC Screener is the agent template you point at your firm's rules. Zyphe MCP is the verification platform under it. Treating them as alternatives produces a procurement gap.
- Audit the data source. The KYC Screener is only as good as the data feeding it. Run the procurement test on the underlying verification platform: sandbox-on-signup, OpenAPI 3.1, signed webhooks, regulator-defensible audit trail. The Zyphe API integration framework applies directly. See our KYC API integration guide.
- Test the policy-import workflow. With Zyphe MCP, the AI assistant can read your firm's existing policies (Notion, Confluence, internal wikis) and apply them to flow configurations. Test this with a representative policy from your team's documentation. See if the resulting Zyphe configuration matches what your CCO would have configured manually.
- Pressure-test the audit trail. Pull a SAR or compliance case from 18 months ago and ask the agent (through MCP) to reconstruct the evidence chain. If the platform produces the case file in minutes with full per-decision triage, the architecture is right. If reconstruction takes hours, the architecture is the problem regardless of which agent runs on top.
- Update procurement documentation. Whether you deploy Anthropic's KYC Screener, an internal agent, or a different vendor's agent, the underlying verification platform's regulator-defensibility is what the regulator audits. Document the platform choice with the same rigor you would document the agent choice. Both layers go in the DPIA.
The bottom line
Anthropic's KYC Screener and Zyphe MCP are complementary. The KYC Screener is the reasoning layer (agent template plus firm-rules skill). Zyphe MCP is the verification platform (regulated identity verification, sanctions screening, UBO walking, decentralised PII storage, AMLA-defensible audit trail). Procurement teams that frame them as alternatives miss the architecture. Procurement teams that combine them correctly get agent-driven compliance work over real, regulator-defensible data.
See how Zyphe MCP works under any AI agent, book a demo or read the launch news article.
Related resources
- Zyphe MCP launch news article, Talk to your compliance stack
- AML transaction monitoring 2026, What the regulations require
- KYC API integration, 15-minute integration guide
- Decentralised KYC primer, What it is, how it works
- KYB software guide, How to verify businesses
- Perpetual KYC, Why one-time KYC fails
 Michelangelo Frigo(Co-Founder at Zyphe)Michelangelo Frigo is a privacy and identity infrastructure expert and co-founder of Zyphe.
Michelangelo Frigo(Co-Founder at Zyphe)Michelangelo Frigo is a privacy and identity infrastructure expert and co-founder of Zyphe.